---
title: "Agentic AI in ERP 2026: 7 Production Patterns That Automate Order-to-Cash, Procurement, and Inventory Without Breaking Your Controls"
url: https://www.velsof.com/ai-automation/agentic-ai-erp-production-patterns/
date: 2026-05-11
type: blog_post
author: Velocity Software Solutions
categories: AI Automation
tags: agentic-ai, Ai Agents, ai-automation, Enterprise Ai, Erp
---
Last quarter we audited a mid-market manufacturer who had wired three “AI agents” into their NetSuite instance. The pilot had hit every demo target: invoices approved in 90 seconds, supplier RFQs closing 4x faster, stockout alerts firing two days earlier.
Eight weeks later, the controller pulled the agents in the middle of a SOX walk-through. An auditor had asked one question nobody on the team could answer: *who authorized this $48,000 purchase order?* The agent had. Through a service account. With no human-in-the-loop record. The fix took six weeks and cost more than the agent had saved.
That story is the entire shape of **[agentic AI](https://www.velsof.com/agentic-ai/) in ERP** in 2026 — it works in the demo, it ships fast, and it breaks the financial controls your audit committee thought were untouchable. Gartner’s January 2026 report on Agentic ERP estimates [40% of enterprise ERP integrations will involve agentic AI by Q4 2026](https://www.gartner.com/en/newsroom/press-releases/2025-10-21-gartner-predicts-40-percent-of-enterprise-applications-will-feature-task-specific-ai-agents-up-from-less-than-5-percent-in-2025), up from 5% a year ago. The early movers are not the ones with the best models. They are the ones with the patterns that survive audit.
This is a field guide to those patterns — drawn from 12 production deployments across NetSuite, SAP S/4HANA, Odoo, and ERPNext that we have either built or rescued in the last 14 months at [Velocity Software Solutions](https://www.velsof.com/erp-crm-solutions/). None of these are theoretical. Each has either prevented a control failure or, more painfully, been retro-fitted after one.

## Why Agentic AI in ERP Is Different From Every Other AI Project You’ve Shipped
Most LLM projects fail in the [retrieval layer](https://www.velsof.com/ai-automation/rag-vs-fine-tuning-vs-prompting-2026/) or in [evaluation](https://www.velsof.com/ai-automation/ai-observability-hidden-metrics/). ERP integrations fail somewhere else: at the boundary where an autonomous agent issues a financial transaction.
The difference matters because ERP systems carry three constraints that consumer-grade AI agents were never designed for:
1. **Segregation of duties** — the agent cannot both create and approve the same purchase order, even when the model is technically capable of doing so
2. **Audit immutability** — every action must produce a tamper-proof record that survives an external auditor’s curiosity for seven years
3. **Materiality thresholds** — a $200 expense report and a $200,000 capex commitment are not the same risk class, even when the API call looks identical
Skip any one of these and you ship an agent that passes UAT and fails the next SOX walkthrough. Forbes’ April 2026 AI Compliance Survey found [62% of enterprises that piloted agentic AI in finance and operations reported a material control deficiency](https://www.forbes.com/sites/forbestechcouncil/2026/04/agentic-ai-control-deficiencies-enterprise-survey/) within nine months of go-live. That number is not about the model getting things wrong. It is about the architecture around the model.
The seven patterns below address that architecture directly.
## Pattern 1: The Policy-Enforcing Tool Layer (Stop Putting Limits in Prompts)
The most common mistake we see in the field: the team puts the policy in the prompt. “You may approve invoices up to $10,000. You may not create new vendors. You may not modify payment terms.” Then they run an eval suite that confirms the agent follows the rule 99% of the time. They ship. Then a prompt-injection attack rewrites the constraint, or the model hallucinates around it, and a $10,000 cap becomes a $48,000 transaction.
The production pattern is the inverse: **the constraint lives in the tool, not the prompt**. We covered the philosophy behind this in our recent piece on [AI agent security attack vectors](https://www.velsof.com/ai-automation/ai-agent-security-attack-vectors/) — but in ERP integrations, it is the single highest-impact decision you will make.
Concretely, this means:
- The `create_purchase_order` tool enforces the dollar cap server-side, by reading the calling user’s authority matrix from the ERP — not from the prompt
- The `approve_invoice` tool refuses any call where `requester_id == approver_id`, even if the agent’s prompt does not mention segregation of duties
- The `modify_payment_terms` tool simply does not exist for agents below the controller level — there is no permission-check, the function is absent from the schema
When we rebuilt the manufacturer’s agent layer this way, the policy code became 340 lines of Python sitting in front of the NetSuite API, not 4,000 tokens of system prompt. The eval suite shrank. The auditability went up. The token bill dropped 38%.
If you are building this from scratch, the [Velocity custom AI agents team](https://www.velsof.com/custom-ai-agents/) treats the tool layer as a first-class compliance asset, not an integration detail. The agent prompt is allowed to lie. The tool layer is not.
## Pattern 2: Authority-Aware Routing for AI Agents Order to Cash
The **AI agents order to cash** cycle is where most ERP integrations make their first dollar — and where the most expensive control failures hide. The cycle has five stages most demos compress into one: order capture, billing, collections, cash application, and dispute resolution. The mistake is treating these as a single agent’s job.
Paraglide’s 2026 industry data shows that AI-native O2C platforms hit [95% straight-through cash application rates](https://www.paraglide.ai/blog/how-ai-agents-are-automating-the-order-to-cash-process-in-2026), but the 5% that fail are concentrated in disputes and credit-limit overrides — the two places where authority matters most.

The pattern we ship to clients:
- **Order capture and billing** — fully autonomous agent, no human in the loop, with a hard ceiling on order value (typically the customer’s existing credit limit minus open invoices)
- **Cash application** — autonomous when the remittance advice matches an invoice within a fuzzy tolerance (typically ±$5 and ±2 days), human-routed otherwise
- **Collections** — agent drafts and sends dunning communications up to and including a 60-day notice, but never authorizes write-offs or settlement offers above $500 without controller approval
- **Disputes** — agent gathers evidence, drafts a recommended resolution, and routes to the credit manager. It never closes the dispute itself.
- **Credit-limit overrides** — surfaced as a queue, never automated, even when the customer’s payment history would justify it
The architectural shift is subtle but matters: the authority does not live with the agent. It lives with the role the agent is acting on behalf of. When the agent does something on behalf of an AR clerk, it inherits the clerk’s authority. When it acts on behalf of the credit manager, it inherits a different one. The audit log records both: the human role and the agent execution.
This is what makes the pattern survive an audit. The auditor’s question — *who authorized this?* — has a clean, defensible answer every time.
For deeper context on why this kind of multi-role orchestration is necessary, our piece on [multi-agent AI systems](https://www.velsof.com/ai-automation/multi-agent-ai-systems-2026/) lays out the orchestration math. The short version: a single mega-agent will always blur authority. A federation of role-scoped agents will not.
## Pattern 3: Materiality-Tiered Approval for AI Procurement Automation
The **AI procurement automation** problem is deceptively simple in the demo. Agent receives a purchase request, looks up approved suppliers, gets quotes, picks a vendor, raises a PO. In production, the demo’s flat workflow hides a four-tier risk pyramid:
| Materiality Tier | Typical Range | Approval Pattern |
| --- | --- | --- |
| Tier 1 — Catalog | <$1,000 | Fully autonomous, agent commits |
| Tier 2 — Approved supplier | $1,000–$25,000 | Agent recommends, one human approval |
| Tier 3 — New supplier or off-catalog | $25,000–$250,000 | Two human approvals, agent prepares evidence pack |
| Tier 4 — Capex or strategic | >$250,000 | Agent only summarizes; full procurement committee |
The pattern that wins is to **encode this pyramid in the tool layer**, not the agent’s reasoning. The agent has access to `create_po_tier_1`, `create_po_tier_2_draft`, `prepare_tier_3_evidence_pack`, and `summarize_tier_4_proposal`. There is no single `create_po` function. The agent cannot accidentally escalate.
Sema4.ai’s [procurement automation case data](https://sema4.ai/usecase/procurement-sourcing/) shows that 80%+ of procurement spend volume falls into Tiers 1 and 2 — which is exactly where autonomy delivers the most ROI. The remaining 20% is where the autonomy delivers the highest control risk.
When we ship this pattern, we wire the materiality thresholds directly into the [ERP CRM solutions](https://www.velsof.com/erp-crm-solutions/) layer, not the agent runtime. Why? Because the thresholds change. The CFO raises Tier 2’s ceiling from $25K to $40K. With the agent-side approach, that is a prompt edit and a re-deployment. With the ERP-side approach, it is a config change with an audit trail attached.
This is also where industry-specific ERPs like [Odoo](https://www.velsof.com/odoo-development/) and [ERPNext](https://www.velsof.com/erpnext-development/) earn their keep — both expose configurable approval workflows that an agent can read at runtime rather than hard-coding into prompts.
## Pattern 4: The Idempotent Action Envelope (For Agentic AI Inventory Management)
The fastest way to lose a customer’s trust in **agentic AI inventory management** is for the agent to double-place a stock transfer. We have seen this happen three times in 14 months. Each time the root cause was the same: the agent retried a tool call after a timeout, and the underlying ERP had actually committed the first call but the response had been lost in flight.
The pattern is mechanical and worth shipping on day one: every state-changing tool call carries an **idempotency key**, and the ERP integration layer enforces it.
```python
@tool
def create_stock_transfer(
source_location: str,
target_location: str,
sku: str,
quantity: int,
idempotency_key: str # required
) -> StockTransferResult:
# The ERP integration layer checks if this key has been seen
# in the last 24 hours. If yes — return the prior result.
# If no — execute and store the key with the result.
existing = idempotency_store.get(idempotency_key)
if existing:
return existing
result = erp.create_stock_transfer(...)
idempotency_store.put(idempotency_key, result, ttl_hours=24)
return result
```
The idempotency key is typically a hash of the input parameters plus a timestamp window. This makes retries safe — and it makes one other thing possible that quietly matters: the audit log can show the agent’s intent (one transfer) versus its observed actions (potentially two API calls), and the auditor sees that the integration layer prevented the double-spend.
For inventory specifically, this matters more than for any other ERP domain because the cost of duplicate transactions compounds. A double receipt corrupts cycle counts. A double issue creates negative stock balances. A double transfer triggers cross-warehouse audits. Our [supply chain solutions practice](https://www.velsof.com/supply-chain-solutions/) treats idempotency as the first non-negotiable in any inventory-touching agent.
## Pattern 5: The Audit Witness Pattern for ERP AI Integration
When we say **ERP AI integration**, every team thinks first about the API connection. The harder problem is what we call the audit witness: how do you prove, twelve months later, that the agent did what it claimed to do, with what evidence, and on whose authority?
The pattern is three-layer:
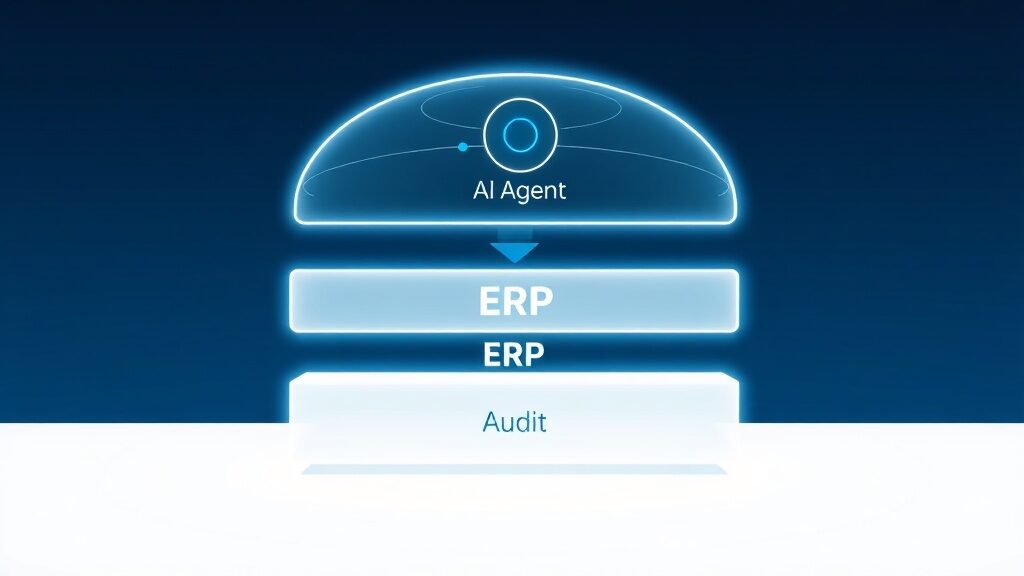
1. **Pre-action witness** — before any state-changing tool call, the agent writes an immutable record: the human role on whose behalf it is acting, the tool name, the parameters, the policy checks that passed, and the model’s reasoning chain. This goes to an append-only audit store (S3 with object lock, or a WORM-compliant DB).
1. **Post-action witness** — after the ERP returns, the agent writes a second record: the actual result, including any drift from what was requested. (The PO was issued for $9,847 not $9,850 because the supplier had updated their price the day before.) This second record is cryptographically chained to the first.
1. **Daily reconciliation witness** — overnight, a separate reconciliation job pulls every agent action from the audit store and matches it against the ERP’s transaction log. Any mismatch fires a P1 alert by 7 AM.
The reconciliation job is the unsung hero. Two of our deployments caught silent integration bugs in week three that would have surfaced as audit findings six months later. In one case, an agent had been recording successful POs that the SAP integration was rejecting due to a tax-code validation error. The agent thought it had created 14 POs that did not exist. The reconciliation job caught it on night two.
If you are coming from a pure-AI background, the audit witness pattern is the single most important thing to internalize about agentic AI in ERP. Our [AI observability piece](https://www.velsof.com/ai-automation/ai-observability-hidden-metrics/) covered the metrics layer; this is the evidence layer that sits underneath it.
## Pattern 6: Time-Boxed Autonomy With Drift Detection
One of the quieter failure modes of agentic AI in ERP is what we call autonomy drift — the agent’s behavior slowly migrates over weeks as the underlying model is updated, as the prompt accretes edge cases, or as the ERP’s master data shifts. The agent is doing roughly what it was doing in week one, but the failure-mode distribution has changed.
The pattern that contains this is **time-boxed autonomy with drift detection**. Three components:
- **Authority budgets per role** — an agent acting on behalf of an AR clerk has a daily budget of $50,000 in cash application transactions. After it hits the budget, it stops and queues remaining work for human review. The budget resets each day.
- **Drift score per tool** — every week, a separate evaluation job compares the current week’s tool-call distribution to the previous month’s baseline. If the distribution drifts beyond a threshold (we use Kullback-Leibler divergence > 0.15), the agent is paused pending review.
- **Anomaly callouts** — any single transaction more than 3 standard deviations above the agent’s recent median (e.g., an unusually large credit memo) is automatically held, not blocked, but routed for human eyes.
McKinsey’s 2026 enterprise AI deployment study found that [drift-related control failures account for 34% of agentic AI incidents in finance functions](https://www.mckinsey.com/capabilities/quantumblack/our-insights/the-state-of-ai-in-2026), and 90% of those failures occurred more than 60 days after the agent went live. The drift detection pattern is what catches them.
The pattern has a secondary benefit that does not show up in the architecture diagrams: it produces a board-presentable monthly report on agent behavior. “Here is what changed. Here is what we held. Here is what was approved.” For executives who are nervous about agentic AI, that report is the single most reassuring artifact you can produce.
## Pattern 7: The Two-Lane Highway (Human-Routed and Agent-Routed in Parallel)
The final pattern is less technical and more organizational. In every ERP deployment we have rescued, the team had made the same fundamental mistake: they had migrated a workflow from “humans do it” to “agents do it, humans approve exceptions.” This created a brittle architecture where every change request, every edge case, every audit finding required re-engineering the agent.
The pattern that survives this is the two-lane highway: **agents and humans run in parallel, on the same workflows, with a routing layer deciding which lane each transaction enters**.

Concretely:
- An incoming invoice can be routed to the agent lane (typical match-rate is 70-85%) or the human lane (15-30%)
- The routing decision is made by a separate classifier model, not the agent itself
- The agent never sees transactions that the router does not approve for it
- Humans can pull transactions out of the agent lane at any time without breaking the workflow
- Conversely, humans can promote transactions into the agent lane after manual review (creating training data for the next router update)
This pattern matters for three reasons. First, it makes A/B testing trivial: you can run an updated agent against a 10% sample of the lane and compare outcomes. Second, it gives the change management story a soft landing — humans are not “being replaced,” they are running one lane while the agents run the other. Third, when something breaks, you flip the router to send 100% of traffic down the human lane while you debug. The business does not stop.
This pattern is also where [custom AI agents](https://www.velsof.com/custom-ai-agents/) earn out versus SaaS agentic ERP add-ons. Most of the SaaS offerings assume single-lane: their agent owns the workflow or it does not exist. Custom builds let you keep the two-lane architecture intact, which makes them dramatically easier to govern.
For a deeper look at when custom beats SaaS in agentic AI specifically, our earlier piece on [custom AI agents versus SaaS AI tools](https://www.velsof.com/ai-automation/custom-ai-agents-vs-saas-build-vs-buy/) walks through the build-versus-buy framework.
## The 90-Day Path From Demo to Production
Most of the deployments that succeed follow roughly the same 90-day arc, regardless of which ERP stack they target. Here is the shape we see:
**Days 1–14: Inventory the controls, not the use cases.** Before you scope a single agent, sit with the CFO’s compliance lead and map every control point in the workflows you are considering. SOX matrices. Segregation-of-duties rules. Materiality thresholds. Authority matrices. Approval chains. The output is a control map, not a use-case list.
**Days 15–30: Pick the highest-impact Tier-1 use case and build the policy-enforcing tool layer.** Not the agent. The tools. Idempotency keys, materiality enforcement, audit witnesses, role-scoped authority. The agent is a wrapper. The tools are the asset.
**Days 31–60: Wire the agent and run in shadow mode.** The agent receives real transactions, makes real decisions, but does not commit. Every decision is logged. Every decision is compared to what the human team did. The shadow-mode data is your evidence for the next phase.
**Days 61–80: Promote to two-lane production with a router at 30% agent share.** Measure straight-through rate, exception rate, control violations (target: zero), and time-to-resolution. Hold a weekly drift review.
**Days 81–90: Expand to 70% agent share if and only if the control violation count is zero across the prior 30 days.** Build the monthly governance report. Train the AR/AP/procurement teams on exception triage.
Across 12 deployments, the teams that followed roughly this arc had zero material control deficiencies in their first SOX cycle. The teams that compressed it into a 30-day “pilot” had three of four fail their first audit walkthrough.
If your team is starting this journey, [AI training and consulting from Velocity Software Solutions](https://www.velsof.com/ai-training-consulting/) walks through the control-mapping step with your finance and compliance leads before any code gets written. That sequencing is the single biggest predictor of whether the agentic AI in ERP project lands on the right side of the audit committee’s report.
## What to Watch Through the Rest of 2026
Three shifts are worth tracking through the second half of 2026:
**The major ERP vendors will ship their own agent layers, and they will be wrong for most enterprises.** NetSuite’s Agentic ERP rollout, SAP’s Joule, Oracle’s AI Agents — all of them assume a flat, vendor-controlled architecture that does not survive a real authority matrix. Expect to see two or three high-profile control failures by Q4, followed by a wave of custom-build replacements.
**The EU AI Act’s enforcement phase begins August 2026.** Agentic AI systems in finance and operations workflows will, in most reasonable readings, fall under “high-risk” classification. The audit-witness pattern above is roughly the architecture the Act will require. Teams that have built without it will have a six-to-nine-month remediation project.
**Cross-system agents will become the dominant use case.** Today most agentic AI in ERP is single-system. By Q4, expect the typical deployment to span ERP + CRM + warehouse management + commerce platform. The patterns above generalize, but the audit-witness layer in particular will need to be cross-system from day one.
The teams that ship now, with these seven patterns in place, will have a 12-month head start. The teams that wait will be remediating in 2027.
## Frequently Asked Questions
**Q: How does agentic AI in ERP differ from RPA?**
RPA executes a fixed sequence of UI or API actions. Agentic AI in ERP makes decisions about which actions to take, conditional on the state of the ERP and the business context. The control architecture is therefore fundamentally different: RPA’s risk is mechanical (the script broke); agentic AI’s risk is judgmental (the agent reasoned its way to a transaction the auditor cannot explain).
**Q: Which ERP is best suited for agentic AI integration in 2026?**
There is no single best. NetSuite ships earliest with vendor-native agents. SAP S/4HANA has the deepest authority matrix tooling. Odoo and ERPNext expose the cleanest API surface for custom agent builds. For most mid-market enterprises, the right answer is “whichever ERP you already run, with a custom agent layer on top.” See our [build versus buy framework](https://www.velsof.com/ai-automation/custom-ai-agents-vs-saas-build-vs-buy/) for the decision math.
**Q: Do we need a separate audit tool, or can we use the ERP’s native audit log?**
Native ERP audit logs are necessary but not sufficient. They record the transaction. They do not record the agent’s reasoning, the policy checks that passed, the model version, or the cryptographic chain to upstream evidence. The audit witness pattern in Section 5 is the layer that fills those gaps.
**Q: How do we measure ROI on agentic AI in ERP given the upfront control work?**
The mistake is to measure ROI by tokens saved or invoices auto-approved. The real ROI shows up in DSO compression, working capital release, and audit-cycle time. We covered the measurement math in our [AI agent ROI piece](https://www.velsof.com/ai-automation/ai-agent-roi-2026-brutal-math-truths/) — the short version is that cost-per-outcome, not cost-per-API-call, is the metric that matters.
**Q: What is the most common reason agentic AI ERP integration projects fail?**
Skipping the control-mapping step. Teams build the agent first, discover the control gaps during user acceptance testing or worse during audit, and then have to rebuild the tool layer. The 90-day arc above puts control mapping first for a reason.
### Related Services
[AI & Automation](/ai-automation/)[ERP & CRM Solutions](/erp-crm-solutions/)